Skip to end of metadata
Go to start of metadata
You are viewing an old version of this page. View the current version.
Compare with Current
View Page History
« Previous
Version 66
Next »
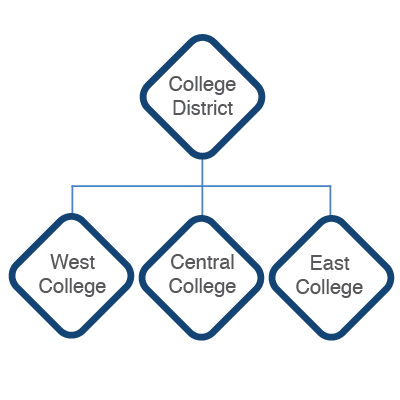
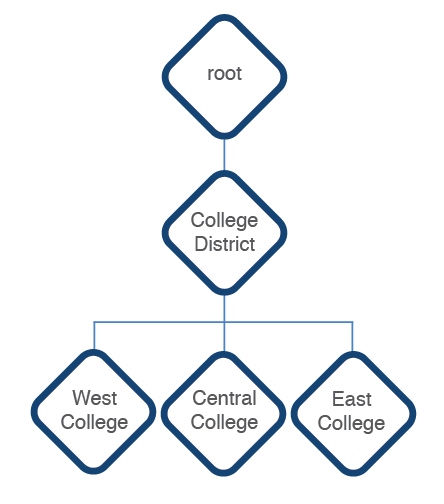
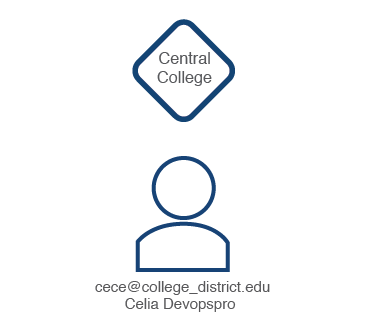
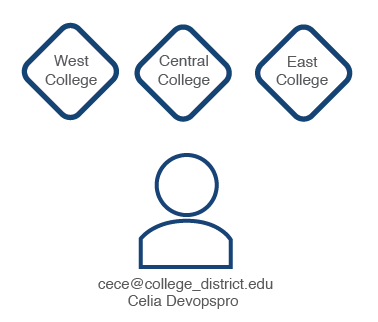
YOUnite groups an organization's master data resources by the organization's structure (e.g. divisions, departments, districts, etc) and uses these groupings to create relationships within the organization. With YOUnite these groupings are called zones.
It's important to gain the distinction that:
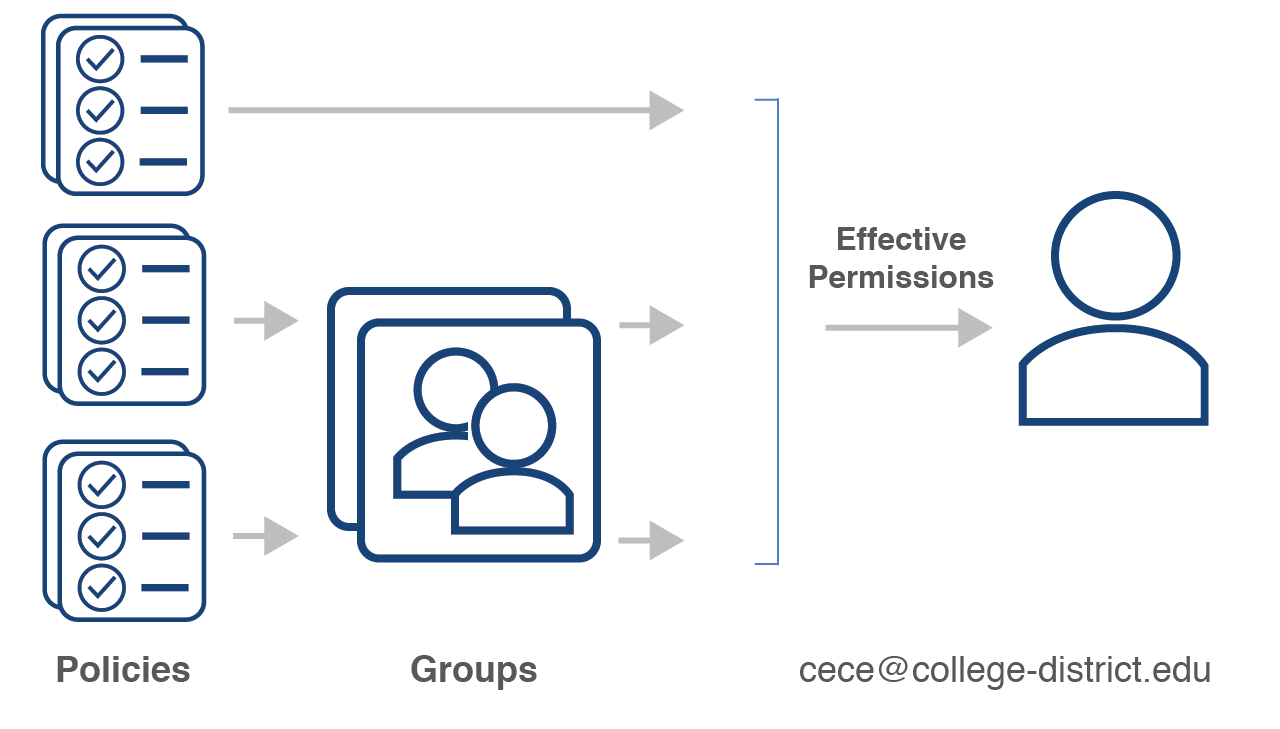
- Access to resources is granted through permissions
- Access to master data is granted through scopes and metadata (covered in the Scopes and Metadata pages).